mirror of
https://github.com/a0rtega/pafish
synced 2024-11-24 07:09:44 +03:00
Add reverse Turing tests, which mimick checks found in real world samples like the UpClicker trojan, leaked source code of Ursnif/Gozi, a "DarkRiver" dropper, the MyWeb-backdoor and XLM 4.0-macros used as droppers. |
||
|---|---|---|
| .github | ||
| pafish | ||
| screenshots | ||
| .gitignore | ||
| CHANGELOG | ||
| LICENSE.txt | ||
| pafish.exe | ||
| README.md | ||
| Vagrantfile | ||

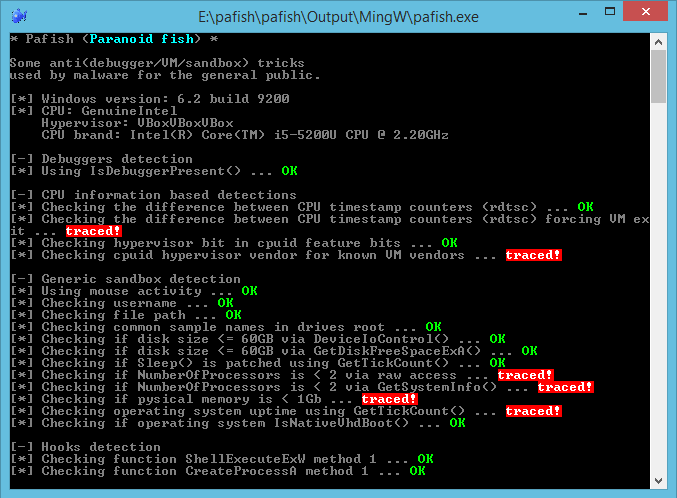
Pafish
Pafish is a demonstration tool that employs several techniques to detect sandboxes and analysis environments in the same way as malware families do.
The project is open source, you can read the code of all anti-analysis checks. You can also download the executable of the latest stable version.
Scope
The objective of this project is to collect usual tricks seen in malware samples. This allows us to study them, and test if our analysis environments are properly implemented.
Build
Pafish is written in C and can be built with MinGW (gcc + make).
Check out "How to build" for detailed instructions.
Author
Alberto Ortega